Cloud Cybersecurity: 5 Tips for 2022 and Beyond
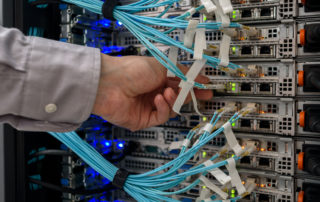
For many enterprise organizations, connecting users and their devices with important information and services means relying on internal IT networks and infrastructure. This reliance can be costly and lead to downtimes when things go wrong. Businesses turn to the cloud for better support and infrastructure, but they still require protection from potential threats and malicious actors who want to gain access ...