Cybersecurity Tools
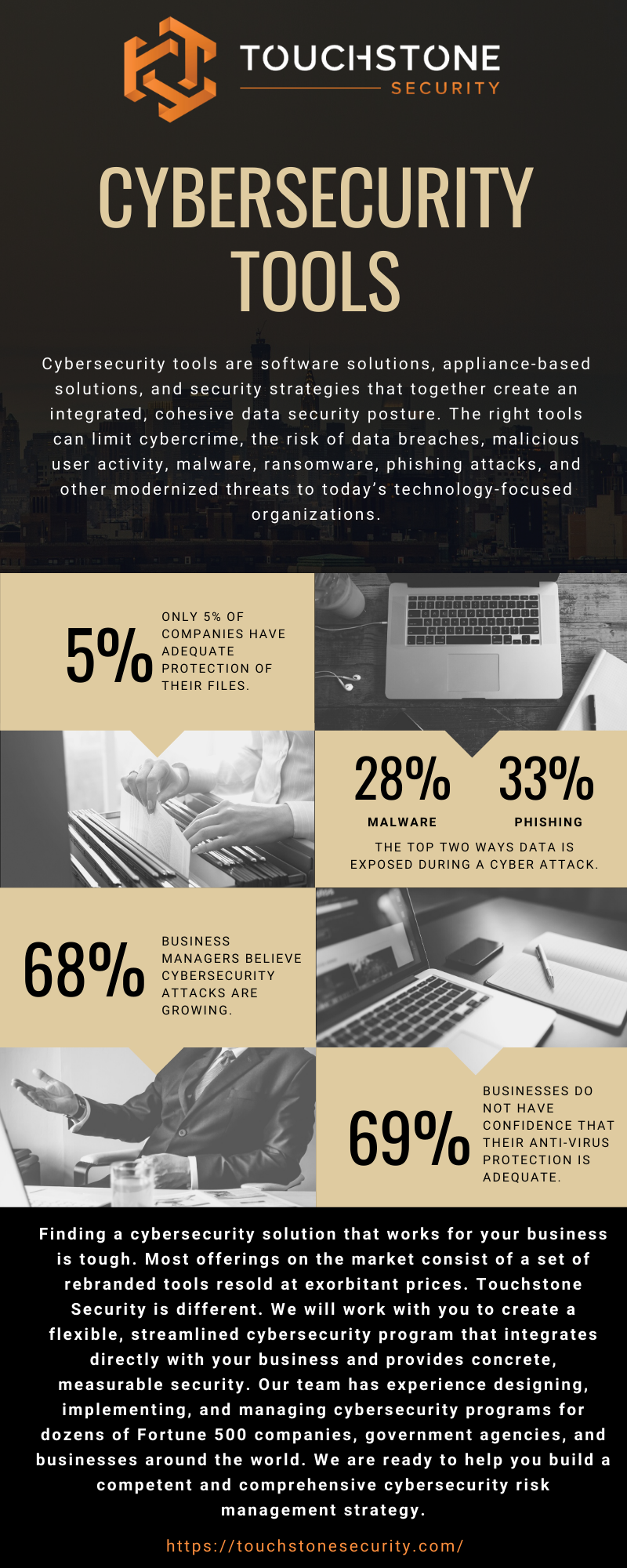
Cybersecurity tools are software solutions, appliance-based solutions, and security strategies that together create an integrated, cohesive data security posture. The right tools can limit cybercrime, the risk of data breaches, malicious user activity, malware, ransomware, phishing attacks, and other modernized threats to today’s technology-focused organizations.
Why Do Organizations Need Cybersecurity Tools?
Today, modern business is becoming more technology-dependent than ever before. Every facet of today’s businesses is becoming more interwoven with technology solutions to support daily business functions. The increased adoption of technology has provided incredible opportunities including reaching new customers in unique ways, creating more efficient channels of communication internally and externally, and allowing for growth into a global interconnected economy.
However, all of these wonderful opportunities come with additional considerations. As an organization becomes more technologically enabled, they also increase their security risks. Cybercriminals are constantly looking for new ways to expose security vulnerabilities within an organization through a technology-based channel such as an email phishing attack or a network breach. As organizations grow to become more technologically enabled, they must also invest in the proper cybersecurity tools to ensure their environments are safe.
Penetration Testing
Penetration testing is a non-malicious data security practice that attempts to penetrate an organization’s security infrastructure with the intention to reveal a security vulnerability. The intended outcome of penetration testing is to provide a vulnerability assessment to the organization so it can enhance its existing security posture before a real security event occurs.
Often, security teams or cybersecurity professionals will implement the same techniques as cybercriminals and hackers as a way to detect vulnerabilities. A penetration test creates an initiative to improve upon security systems and plugins. It can also help fix misconfigurations, enhance internet security, limit the downloading of suspicious or free software, and improve access control. Following a successful penetration test, organizations may enter a period of auditing to ensure that the security improvements are indeed effective to minimize the risk of a cyber attack.
Network Security
Network security is another component of a modernized data security posture to protect sensitive data and IP. Network security builds on a collection of software-based and hardware-based security solutions to monitor network traffic and mitigate security risks transmitted over an internal network. Here, security components such as intrusion detection systems (IDS) and intrusion prevention systems (IPS) monitor and remove suspicious activity in real-time transmitted within an organization’s network. These systems use an advanced analyzer built on the principles of machine learning to detect unusual patterns of data transmitted over a network. These vulnerability scanners act as a critical component of any modernized security posture.
Cybersecurity tools: Firewalls
An organization’s firewall is one of the most critical components within a modern IT environment today. The firewall acts as the wall protecting an internal network from the outside world. Firewalls dictate which communication ports are opened and validated to transmit data between the internal network and the outside world. Firewalls use advanced algorithms to constantly monitor the defined ports for suspicious data attempting to enter an environment. Should the firewall detect an abnormality, it can remove the data packet, neutralizing an attack before it enters the protected environment.
Cybersecurity Tools: Anti-Malware
Malware is one of the most prominent vectors for an attack on an organization’s sensitive valuable data today. Malware is a broad term that describes any malicious software that once installed is designed to exploit a user or organization. There are many different types of malware such as viruses, ransomware, spyware to mention a few. All of these various types of malware are designed to steal sensitive information or prohibit the data owner from accessing the sensitive information until they pay a ransom (in the example of ransomware). Users often inadvertently download malware when using unsupported web applications, downloading open-source software, or downloading other purported free tools. To address these challenges organizations often implement a third-party antivirus software or backup solution to create protection and redundancy in their protected IT environment.
Mobile Protection Tools
Mobile protection is becoming increasingly important for organizations as they look to limit the attack vectors for malicious attacks. Mobile phones such as Apple, Microsoft, or Android smartphones can act as a security risk when they connect to an organization’s internal network to use an organization’s wi-fi rather than their provider’s wireless network to access the internet. In this scenario, as users access the public internet cybercriminals can gain access to the mobile device and from there access to the organization’s sensitive information. Often, third-party software tools can be installed on the mobile device itself to minimize the threat of security threats through limiting access to an internal network or scheduling vulnerability scanning designed to target and remove security threats.
